MalDev
EIKAR test file:
$ msfvenom -p windows/messagebox TITLE="EICAR" TEXT="X5O!P%@AP[4\PZX54(P^)7CC)7}$EICAR-STANDARD-ANTIVIRUS-TEST-FILE!$H+H*" -f raw -o eikar.binBlog Series / Books
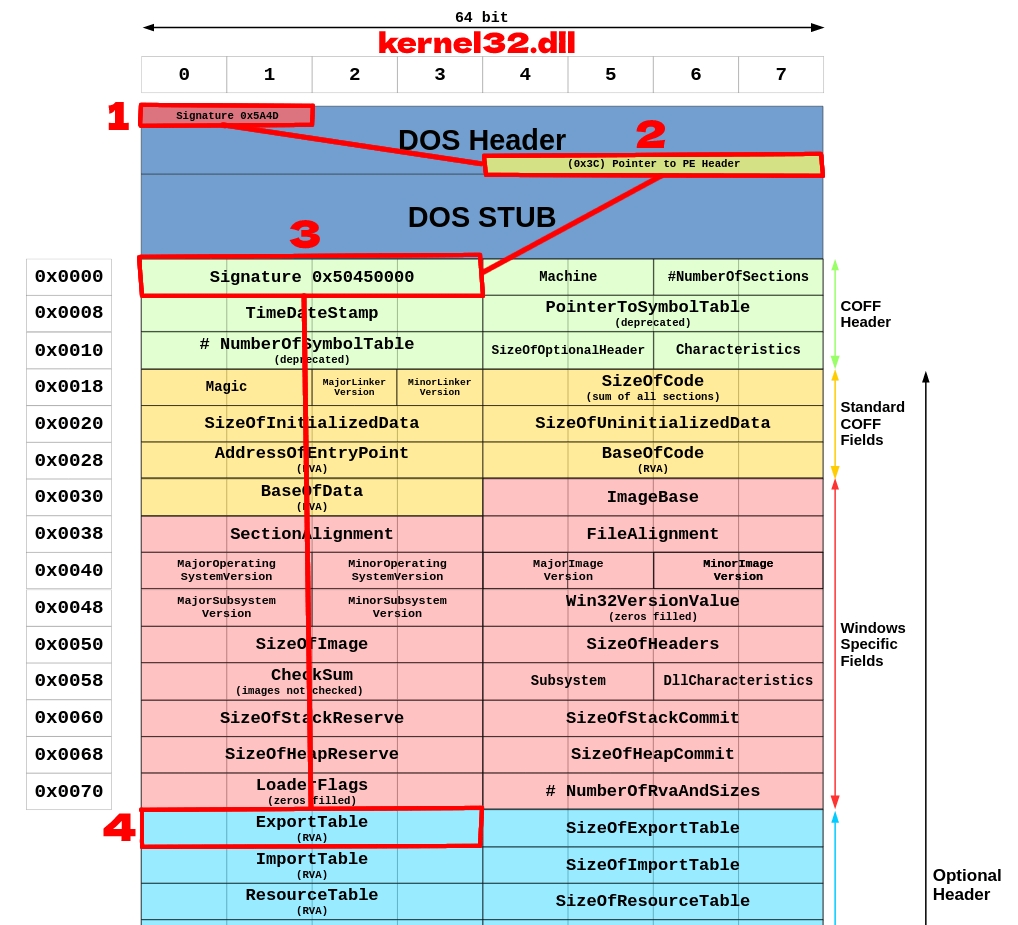
PE Structure (+ PEB/LDR)
A dive into the PE file format (0xRick)
Malware development (0xPat)
Windows APT Warfare (Sheng-Hao Ma)
Malware Development for Dummies (Cas van Cooten)
Learning LLVM (sh4dy)
Last updated